Summary: In this Article, you’ll get to read about —

While remote work exacerbates the use of personal devices cloud-based services are gradually becoming the cornerstone of every industry where the amount of data businesses must store and possess skyrocketed.
Nowadays, when external attacks such as hacking, phishing, and ransomware are getting much attention, how companies manage data internally is also a vital aspect of data protection.
You must be familiar with the term shadow it which is the use of IT-related hardware or software by a person without Its knowledge. But what is Shadow data?
Well, Shadow data refers to the data created, stored, or shared without being formally supervised or governed by suitable IT teams.
So in this read, we will explore simple yet effective strategies to manage and secure shadow data, ensuring your information remains safe and your operations compliant.
Let’s Start!
Understanding Shadow Data
Shadow data refers to information created and stored without explicit organizational approval. It can emerge from various sources like unsanctioned apps, devices, or even well-meaning employees bypassing IT protocols for convenience. The risk? This data, often sensitive, isn’t protected by standard security measures, making it a goldmine for cyber threats. Recognizing its sources and potential dangers is the first step in mitigating its risks.
Strategies for Managing Shadow Data
Managing shadow data is about being proactive—identifying, classifying, and controlling the data before it becomes a security risk. The strategies outlined in this section will set the foundation for a robust approach to dealing with shadow data.
By taking these steps, organizations can significantly reduce the volume of unmonitored and unprotected data, paving the way for more focused security measures:
- Inventory and Mapping: Begin by identifying all data sources within your organization. Use tools designed to detect and map data, including the shadowy kind. Knowing where your data resides is the foundation of managing it.
- Policy Development: Establish clear policies regarding data creation, storage, and management. Make sure these guidelines are easy to understand and follow. They should cover the use of approved software and devices, outlining procedures for introducing new tools into the ecosystem.
- Regular Audits: Conduct audits to ensure compliance with your data policies. These checks help uncover any instances of shadow data, allowing you to address them promptly. Audits also serve as a deterrent against unauthorized data practices.
Securing Shadow Data
With a solid management plan in place, the next necessary step is securing the identified shadow data. Security measures ensure that any sensitive information contained within shadow data is protected against unauthorized access and breaches. This section will explore the key technologies and practices that can help organizations safeguard their shadow data effectively:
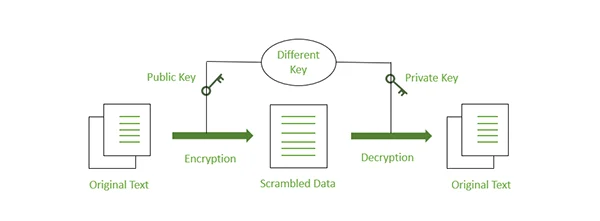
Encryption Techniques
One of the most effective ways to secure any data, shadow or otherwise, is through encryption. Encrypting data changes it into a code that unauthorized users can’t easily read. Ensure that all sensitive data, especially shadow data, is encrypted both at rest and in transit. This adds a robust layer of protection, making it significantly harder for cyber attackers to exploit.
Access Control Measures
Not everyone in your organization needs access to all types of data. Implement strict access controls based on roles and necessity. This practice, known as the principle of least privilege, ensures that employees can only reach the information necessary for their tasks. Such measures minimize the risk of internal and external breaches.
Employee Education and Training
Often, shadow data arises from employees not understanding the risks associated with their actions. Regular training sessions can enlighten your team about the importance of data security and the dangers of creating shadow data. Educating your workforce turns them from potential security liabilities into informed defenders of your organization’s digital assets.
Benefits of Proper Shadow Data Management
Effective shadow data management brings numerous advantages.
Let’s explore these benefits in detail through the table below:
| Benefit | Explanation |
| Enhances Security Posture | Proper management of shadow data strengthens your organization’s defense against cyber threats. This proactive approach significantly lowers the chance of experiencing data breaches. |
| Ensures Compliance | By effectively managing shadow data, your organization can adhere to data protection laws and regulations. This compliance helps avoid legal issues and financial fines that could arise from data mishandling. |
| Fosters Transparency and Accountability | A well-implemented shadow data management strategy promotes a culture where data is handled openly and responsibly. It ensures that all team members understand the importance of security, leading to a more secure and accountable workplace. |
The Role of Technology in Shadow Data Management
In our journey to secure and manage shadow data, technology plays a pivotal role. With the right tools, organizations can automate the detection, classification, and protection of data, making the process both efficient and effective.
- Automated Detection and Mapping Tools: Technology solutions can automatically discover and map data across an organization’s network. These tools are invaluable in identifying shadow data by scanning storage systems and cloud services for unaccounted information. Once identified, organizations can take steps to secure this data.
- Data Loss Prevention (DLP) Software: DLP solutions monitor and control data transfer within a network. They can be configured to prevent sensitive information, including shadow data, from being sent outside the organization without authorization. DLP tools play a vital role in mitigating the risk of data leaks and breaches.
- Cloud Access Security Brokers (CASBs): CASBs are security policy enforcement points placed between cloud service consumers and providers. They ensure that network traffic complies with the organization’s security policies. CASBs can identify unsanctioned cloud services—common sources of shadow data—and enforce security measures to protect data.
Conclusion
Managing and securing shadow data is an ongoing challenge that requires vigilance, clear policies, and a commitment to education. By implementing the strategies outlined above, organizations can mitigate the risks associated with shadow data, protecting their valuable information assets. Remember, in the realm of data security, awareness is the first step to protection. Encourage a culture of openness and continuous improvement to keep your data safe and secure.



